The documents leaked by Edward Snowden and published by the Guardian and other outlets confirm what privacy advocates have been saying for years: The government has secretly turned its most powerful weapons of foreign intelligence surveillance inward on millions of Americans.
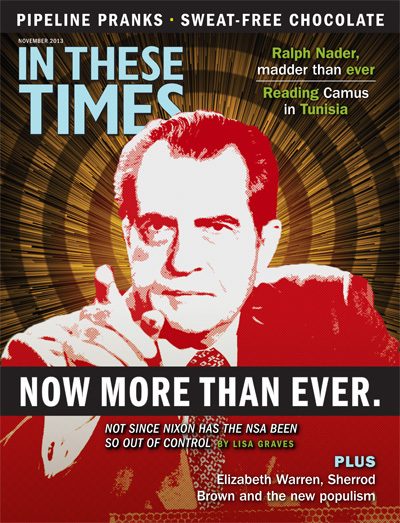
How can an ordinary citizen cut through the brush — with the avalanche of complicated, classified materials released, the flurry of political finger-pointing, and the various denials and narrowly crafted dodges? Welcome to a guided tour of the National Security Agency (NSA) scandal. We’ll explore how we got here and what Nixon’s got to do with it.
Who? Me?
The NSA has rebuffed demands by some in Congress for an estimate of the number of Americans whose information has been gathered, stored and searched, but the math is simple. Unless you are a child, a Luddite or a hermit who has never dialed a phone or used the Internet, records of your phone calls and online interactions have been captured by the NSA.
This includes your number and everyone you dial or text, plus how of- ten and how long you talk, as well as your location — although the NSA has claimed it doesn’t actually use the location data. In other words, the NSA has the fact of all your calls with your friends, family, lover(s), bank(s) and doctors’ offices for whatever ails you, along with calls to psychic hotlines or phone sex workers, if that’s your thing. The number of innocent Americans affected: at least 260 million.
That’s not all. For nearly a decade, the NSA was gathering records about Americans’ “Internet transactions,” including “metadata” such as the “to, from, cc and bcc lines of a standard email,” when your email was sent and opened, your IP address and location, and an array of data about you as you search the Internet, and interact with friends and strangers through social media. That program is no longer authorized by a secret court in Washington, D.C., but whether it continues is unknown. Also unknown: whether the NSA’s gathering of Americans’ credit card transactions is continuing or was secretly stopped.
Even that’s not all. Though the NSA has emphasized that it does not obtain the “contents” of your calls or emails through this program, the government has decided that the contents of all international phone calls and emails “to or from” Americans and others abroad are fair game for acquisition by the NSA without a warrant. At least 40 million American citizens travel internationally each year, and America is home to 40 million immigrants, who call or email their loved ones overseas about their most intimate worries and desires.
And there’s more. Newly declassified documents prove that countless purely “domestic” conversations between innocent Americans here in the United States have also been acquired and searched by the NSA.
Additionally, the affidavits in lawsuits filed in 2006 by the Electronic Frontier Foundation present evidence that shortly after 9/11 the NSA installed “NARUS” devices at AT&T’s main transmission station in San Francisco and at other telecommunications hubs across the country. Those devices are designed to make a duplicate of the communications stream (content and data) as it passes through the system at the speed of light.
Accordingly, such devices can give the NSA access to all American domestic and international phone calls and Internet activity that travel through AT&T, which provides the backbone of the communications system that other phone and Internet service providers rely on. So, as a technological matter, if law were no barrier, the evidence indicates that the NSA could technically acquire, store and analyze almost every word spoken or written on American phones and computers.
Snowden’s revelations include Power Point presentations referencing an array of tools — with code names like “PRISM” — the NSA has used to target the social media activities, Internet searches and emails of specific people. But there’s still a lot we don’t know. And that’s a problem in a democracy in which the government is supposed to govern by consent of the people.
The risk of ‘total tyranny’
Sen. Frank Church (D-Idaho) said after his investigation of the NSA in 1975, following leaks about President Richard M. Nixon’s use of the NSA to spy on his enemies, opponents of the war in Vietnam and others:
If this government ever became a tyrant, if a dictator ever took charge in this country, the technological capacity that the intelligence com- munity has given the government could enable it to impose total tyranny, and there would be no way to fight back because the most careful effort to combine together in resistance to the government, no matter how privately it was done, is within the reach of the government to know. Such is the capability of this technology. … We must see to it that this agency and all agencies that possess this technology oper- ate within the law and under proper supervision so that we never cross over that abyss. That is the abyss from which there is no return.
Those were the late Senator Church’s fears before almost every American had a “smart phone” and before most of us heard of the Internet — which in the 1970s was merely a computer network within the Pentagon and a few Silicon Valley companies — let alone traversed it daily.
Indeed, before Google was a word, let alone an empire; before almost all of our telephone conversations, emails and transactions of daily life were transmuted into a searchable digital world; and before a handful of murderers crashed into the World Trade Center and the Pentagon on September 11, 2001, we needed greater protections for our privacy and liberty.
Now that need is even more urgent.
Along with the seismic transformation in the way we communicate, the legal controls on the NSA’s powers have been systematically loosened, if not obliterated, by the White House, Congress and the courts at the urging of leaders of the military intelligence community.
The NSA says it has “internal controls” but once information about Americans is stored by the NSA — including in a gargantuan 1-million-square-foot data storehouse being finalized in Bluffdale, Utah — it can be accessed by numerous civilians at home and abroad. The agency claims there have been only 12 incidents of NSA staffers using its “Signals Intelligence” (SIGINT) improperly. Most of them spied on lovers, such as girlfriends suspected of infidelity. However, almost all of these were discovered only through polygraph tests of workers renewing security clearances. How many more times have lovers or enemies been “targeted” by government employees, the military and intelligence contractors with access to the trove of SIGINT data?
More importantly, how can we ever trust that the NSA’s new powers won’t be misused by those in power? We already know that during the Occupy Wall Street protests, federal “counterterrorism” dollars were used by the Federal Bureau of Investigation, the Department of Homeland Security and local law enforcement to monitor Americans guilty only of speaking against Wall Street’s destruction of our economy and its corruption of our democracy. And the government got away with it.
So the question isn’t whether the information that the NSA has been allowed to gather on Americans will be misused. The question is, when? And by whom? Perhaps our next president? Religious- Reactionary Rick (Santorum)? Tea Party Ted (Cruz)? Take-Two Rick (Perry)? You may laugh, but remember that prior to the 1980 presidential election, Trees-Cause-More-Pollution-Than-Automobiles Ronald (Reagan) was a joke.
Who in the NSA’s quasi-military hierarchy has the power to question a demand to provide information in its databases about specific Americans when made under the authority of the commander in chief, no matter who the president is or which power-hungry advisors aid the White House in 2016 or 2020 or beyond?
It’s a state of affairs that would make Nixon smirk. It’s also why foreign citizens who’ve lived under authoritarian regimes, in Germany and elsewhere, have expressed some of the greatest horror at the revelations over the NSA’s ubiquitous monitoring.
The past isn’t even past
To understand what happened to the rule of law since 9/11, it’s important to understand the path of the law before the World Trade Center towers fell.
It begins with the Fourth Amendment, which makes no distinction between “intelligence gathering” and “law enforcement.” The Constitution speaks instead to the rights of Americans regardless of the agent that would violate them:
The right of the people to be secure in their persons, houses, papers and effects, against unreasonable searches and seizures, shall not be violated, and no Warrants shall issue, but upon probable cause, supported by Oath or affirmation, and particularly describing the place to be searched, and the persons or things to be seized.
Those words were born of the vanquishing of an authoritarian tyrant whose officers used “general warrants” to search colonists at will to protect the crown and its interests.
Surprisingly, it was not until 1967 that the Supreme Court ruled that the government needed a warrant to listen to Americans’ phone calls. The following year, in 1968, Congress passed a crime bill to provide rules for obtaining warrants for wiretaps but — at the secret urging of the NSA — the legislature exempted surveillance in the name of national security.
In November of that year, Nixon was elected president.
In 1969, just six months after taking office, Nixon directed the NSA to search its files for information on specific Americans whom he and J. Edgar Hoover had placed on a watch list.
At that time, the existence of the NSA, formally established in 1952, was so secret that almost no one in Congress knew about it, and its funding was concealed in the Pentagon’s classified “black budget.” For decades, the NSA and its predecessors had acted as the government’s signal corps, listening for radio communications from enemy ships, tapping into the cables of diplomats of the Soviet Union and decrypting ciphers sent by spies. Unbeknownst to Congress, the NSA and its predecessor, the Armed Forces Security Agency, had also been spying on Americans for decades, making duplicates of all of the international telegrams sent to or from Americans by “wire” or cable since 1945, as well as gathering radio transmissions from across the globe through earth-bound satellite receivers and satellites. By the early 1970s, the NSA’s analysts were reading over 150,000 telegrams to or from Americans a month under that program, called “Operation SHAMROCK.”
With this vast and secret intelligence-gathering apparatus at his disposal, Nixon later expanded his watch list, directing the NSA to search for anything “subversive” or related to drug-dealing. In the meantime, in 1972, a case involving Nixon spying on Americans under the guise of national security, with no link to a foreign government, made its way to the Supreme Court. In that case, known as the Keith case, the Court unanimously declared:
The Fourth Amendment freedoms cannot properly be guaranteed if domestic security surveillances may be conducted solely within the discretion of the Executive Branch. … The Fourth Amendment does not contemplate the executive officers of Government as neutral and disinter- ested magistrates.
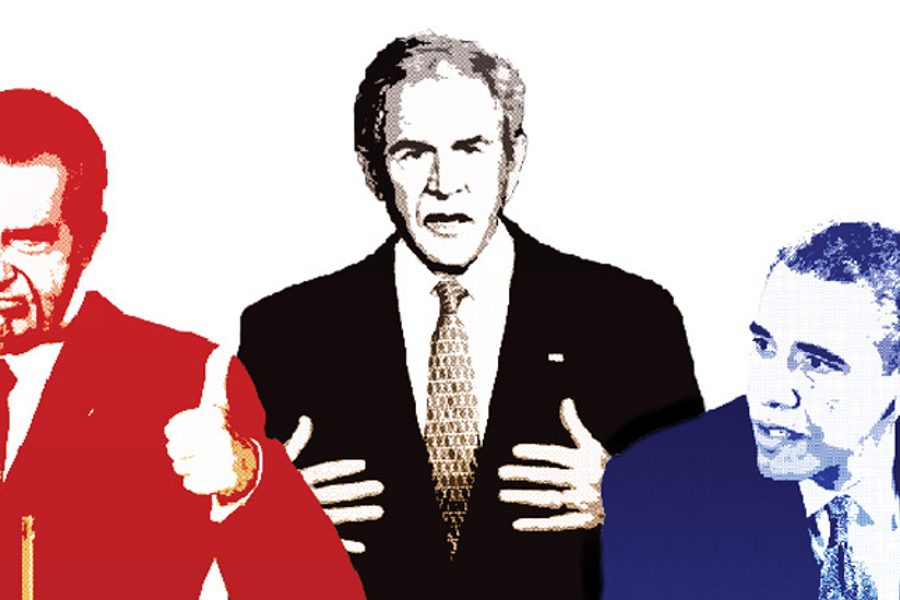
In August 1974, in the wake of the Watergate scandal involving the illegal surveillance activities of the Committee to Re-Elect the President (CREEP), Nixon resigned in disgrace.
Yet the extent of electronic surveillance under the administration wasn’t revealed until December 1974, when the New York Times published a front-page story by Seymour Hersh under the headline “Huge C.I.A. Op- eration Reported in U.S. Against Anti-War Forces.” The article exposed part of Nixon’s spying under a program code-named “Operation MINARET,” which made use of the cables the NSA searched via SHAMROCK and by capturing radio transmissions.
Congress was shocked. During the investigation led by Sen. Church in 1975, Congress discovered that the NSA had access to communications involving millions of Americans and that there were about 1,200 Americans on watch lists, mostly people opposing the Vietnam War.
But the names of some Americans on the watch list were kept sealed until they were released this September. The newly declassified documents reveal that the NSA’s spying targeted prominent Americans even before Nixon took office. According to the National Security Archive, the NSA “eaves- dropped on civil rights leaders Martin Luther King and Whitney Young, as well as boxing champion Muhammad Ali, New York Times journalist Tom Wicker, and Washington Post columnist [and humorist] Art Buchwald”— and Sen. Church himself.
In response to Sen. Church’s investigation, Congress passed the Foreign Intelligence Surveillance Act (FISA) of 1978, over the objections of a few hard-liners in the Ford administration, including Laurence Silberman. It was intended to ensure that the NSA was focusing on foreigners and not on Americans, and “to curb the practice by which the Executive Branch may conduct warrantless electronic surveillance on its own unilateral determination that national security justifies it.”
FISA barred the NSA from inten- tionally acquiring radio signals of the domestic communications of Ameri- cans without a warrant. It also barred the NSA from acquiring wire communications here that were to or from Americans, whether intentional or not. And it barred the NSA from intentionally targeting radio communications to or from a known U.S. person in the country. It also created rules for ob- taining warrants to target Americans, requiring probable cause that a person was knowingly aiding an agent of a for- eign power or someone planning “ter- rorism” or sabotage, as well as short-term rules for emergency or war.
Congress also created a special court, the Foreign Intelligence Surveillance Court (FISC), to hear these warrant requests. At the same time, Congress established permanent Senate and House Intelligence Committees to conduct oversight of the NSA, CIA and more.
Project MINARET and Operation SHAMROCK were said to be terminated when FISA passed, and the public believed such activities were barred. By almost all accounts, the NSA was directing its powerful surveillance tools outside of the United States, discarding Americans’ communications that were not relevant to its operations, and tuning its radio channels to foreign navies and diplomats. Meanwhile, a Soviet reformer named Mikhail Gorbachev came to power, the Cold War thawed, the Berlin Wall fell, and the need for enormous military and intelligence budgets was being questioned.
Then came 9/11.
Checks and balances?
This much is clear: In the weeks following 9/11 a handful of men in the Executive Branch literally rewrote our rights as citizens. While Americans were sold war to secure “freedom” against al Qaeda, our freedoms at home were deliberately undone in the name of protecting us.
That revision of our rights occurred on two fronts. One was a public debate over the Patriot Act, which obscured the second: even more dramatic changes being orchestrated by Vice President Dick Cheney’s office behind the scenes.
As the Pentagon prepared for war in Afghanistan and Congress passed an “Authorization for the Use of Military Force,” the George W. Bush administration sent Congress a wish list of changes to the law that were later titled “Uniting and Strengthening America by Providing Appropriate Tools Required to Intercept and Obstruct Terrorism Act of 2001,” otherwise known as the “USA Patriot Act,” or Patriot Act.
The Patriot Act changed some parts of FISA, but nowhere did it authorize the NSA to acquire all of Americans’ phone or internet records. Nor did it change FISA’s rules to allow Operation SHAMROCK-style monitoring of the content of Americans’ international communications.
While Congress was considering the Patriot Act, the White House had already secretly changed the rules for NSA surveillance on these shores. Arch-autocrat David Addington (Vice President Cheney’s right-hand man) hand-picked one Justice Department official — the newly hired John Yoo — to write a legal memo justifying the NSA surveillance programs that Edward Snowden would expose 12 years later. Yoo wrote a secret memo asserting that the president is not bound by FISA’s legal rules for warrants because he has plenary powers as commander in chief.
Attorney General John Ashcroft, who was busy pushing the Patriot Act, did not even know Yoo had written that memo about what became known as the “President’s Surveillance Program” when he cosigned the president’s first authorization document on Oct. 5, 2001 and the NSA began asking telecommunications companies for access to their switches.
It was two years after the launch of the new NSA surveillance before the White House told even one judge on the Foreign Intelligence Surveillance Court (FISC) about the programs. That judge, the chief judge, was not asked to approve the surveillance and was not allowed to tell the other FISC judges about it.
In 2004, the Justice Department hunkered down to create a new legal memo rationalizing the program as implicitly authorized by the Authorization to Use Military Force in Afghanistan. Later that year, the FISC was asked to approve an order authorizing this surveillance for the first time, and it did.
While this battle was brewing and the presidential election was in full swing, James Risen and Eric Lichtblau of the New York Times were onto a story about the NSA’s domestic surveillance, but the White House claimed the story would hurt national security and risk American lives, and so publisher Arthur Ochs Sulzberger, Jr. held it until more than a year after the election.
On Dec. 16, 2005, the Risen-Lichtblau story broke: “Bush Lets U.S. Spy on Callers Without Courts.” The Bush administration responded by declassifying the least controversial component of the program and rebranding it as the “Terrorist Surveillance Program,” or TSP. As Bush famously quipped in trying to distract from the revelations: “If somebody from al Qaeda is calling you, we’d like to know why.”
In the midst of the uproar over the NSA spying, the Patriot Act was reauthorized in March 2006.
But in May of that year, more leaks came, with USA Today publishing a story that said the NSA was “amassing information about the calls of ordinary Americans — most of whom aren’t suspected of any crime.”
By the time these extraordinary surveillance programs had been operational for six years, nearly 3,000 unelected executive branch employees (and an unknown number in the private sector) knew of the programs, but only 60 out of the 535 members of Congress.
Nevertheless, in 2007, aided by lobbying from telecommunications companies like AT&T — which feared it would be held criminally or civilly liable for violating the Wiretap Act and FISA— Director of National Intelligence Mike McConnell began a full-court press to get FISA changed to give retroactive immunity to the companies and Congress’s blessing to the programs. After a court struck down a portion of the program, McConnell demanded Congress temporarily authorize it through the Protect America Act, which was re- placed a few months later in 2008 by the FISA Amendments Act.
Then-Sen. Obama, despite expressing earlier concerns about the NSA’s warrantless electronic surveillance, supported those bills as he began to seek the White House. As president, he has embraced those (and other) controversial uses of power that were initiated by the Bush administration. Although he immediately sought to shut down Guantánamo, only to be thwarted by Congress, on the issue of NSA spying he has largely continued the programs and defended them. There has been little “change” or “hope” when it comes to protecting Americans’ privacy from the NSA’s surveillance powers. It’s been mostly business as usual under for the NSA, FBI and DHS.
Moreover, in light of the full weight of the Snowden revelations, when one looks at the statutory constraintson the NSA now, the limits in FISA that ostensibly protect Americans’ rights look slippery.
For example, Section 702 of the FISA Amendments Act repeats the traditional rule that the NSA cannot acquire communications that “intentionally target any person known at the time of acquisition to be located in the United States.” Given the revelations, though, does this mean the statute allows targeting of Americans in pools of information after international communications are seized?
Similarly, the NSA “may not intentionally acquire any communication as to which the sender and all intended recipients are known at the time of the acquisition to be located in the United States.” However, at the time an email is transmitted and thus acquired, the NSA could argue that it does not know where all the recipients are located, as a Bush rep argued “hypothetically” to privacy advocates in 2007.
Thus the protections in the FISA statute that at first appear to be shields against spying on Americans, appear upon closer inspection to operate as swords.
Where’s the Fourth Amendment?
Three rulings issued by FISA judges hand-picked by the Chief Justice have narrowly construed people’s Fourth Amendment rights when it comes to two core issues: the rules for content and data acquired by the NSA.
The Bush administration set the stage for its evasion of the Fourth Amendment in 2002, when it asked for a ruling from the FISA Court of Review (FISCR), which oversees FISC, in a case involving a Patriot Act provision changing the purpose of FISA surveil- lance. Judge Silberman (who testified against FISA in 1978) and two other judges heard government arguments— arguments originally concocted by Yoo. Silberman acted like an advocate from the bench, arguing that the Constitution does not require a warrant before the government can acquire the content of Americans’ communications.
The FISCR ruling opined that the constitutional test for searches in intel- ligence cases was “reasonableness,” not a warrant, and “the key to the reason- ableness of any search is the exterior threat.” In 2008, an unnamed “Internet Service Provider” (ISP) challenged “directives” issued after FISA Amendments Act as unconstitutional, but the FISCR ruled that the Constitution did not require a warrant based on probable cause to demand content of communications. In balancing whether a search order was “reasonable” under the Fourth Amendment, the court ruled that national security is of the “highest order of magnitude.”
In the most recent decision issued by the FISC, a lower court judge ruled that the NSA could acquire Americans’ call records en masse because Americans have “no reasonable expectation of privacy” in their phone or Internet data— a claim based on a Supreme Court decision from 1979 that most Americans have never heard of.
In that obscure case, Smith v. Maryland, a robbery suspect named Michael Lee Smith sued the state after police obtained his call records from his phone company without a search warrant. The Supreme Court, dominated by four new Nixon appointees, ruled that Smith had no constitutional expectation of privacy in information about himself conveyed to a third party, such as the phone company. (Justices Thurgood Marshall, Potter Stewart and William J. Brennan, Jr. dissented, noting that using a telephone does not carry with it an assumption that this information will be released to others, let alone the government.)
The FISC embraced this precedent despite dramatic changes in technology since the original decision. In the old days, the numbers you dialed could be obtained by law enforcement through a court order, without accessing the content of the conversation. But in the digital age, if the government has access to the calls as they transit the phone company in fiber optic cables, the government can duplicate the content as it seizes data.
Despite these differences, the FISC ruled that Americans’ electronic call records can be vacuumed up by the NSA.
Additionally, the court servilely stated that the NSA’s computers work best when they have records of all of your calls — so all the call records they must have.
The FISC also claimed that the surveillance was consistent with the statutory rules for access to third party records, as modified by the Patriot Act, which allow courts to order businesses to turn over records “relevant to an authorized investigation.” The court’s order deemed all Americans’ phone re- cords to be relevant to a general investigation to prevent terrorism because any record might be a link to a potential terrorist.
If everything is relevant or potentially relevant, then relevance means nothing.
Now what?
The good news is that Americans are rejecting these rationales and are doing so in a way that transcends traditional political party divides. A growing number of Americans dissent from these policies. Most Americans know they have should have a right to privacy in their communication and Internet records. A growing number of Americans believe that the content of their emails, phone calls and Internet searches should not be given to the NSA if they have done nothing wrong.
No government agency should be allowed to access the backbone of America’s communications infrastructure inside or outside the United States.
Two of the most recent directors of national intelligence, James Clapper (USAF-ret.) and Mike McConnell (USN-ret.) have led efforts to turn the NSA inward on Americans and have misled Americans about the scope of these powers in the name of keeping us safe. Both cashed out their military service with the private-sector consulting firm of Booz Allen Hamilton (Edward Snowden’s former employer) and then moved to top government “civilian.”
Concerns about trusting the NSA are only underscored when the government has been deceptive in its communications with the American people and with congressional and judicial overseers. In March, Sen. Ron Wyden (D-Ore.) asked Clapper: “Does the NSA collect any type of data at all on millions or hundreds of millions of Americans?” Clapper replied stoutly, “No, sir.”
This denial was exposed as a demonstrable lie four months later, when the Snowden materials surfaced.
The NSA should only be allowed to access the contents of Americans’ calls or emails based on an individualized warrant predicated on probable cause of wrongdoing. As for international calls and emails to or from an American, they should be subject to the requirement of an individual warrant on one end before they can be searched.
No American’s name should be queried in the NSA database of calls, emails and Internet searches without an individualized warrant.
Americans’ phone and Internet data should not be acquired at all, unless it is directly connected (in one or two hops) to a specific person who is a legitimate target of a terrorism or espionage investigation.
We also need better protections for information we have already “shared” with a company — including the data that trails you as a result of digital communications — to protect our inherent right to privacy against both the private sector and government.
As Sen. Sam Ervin (D-N.C.) — a staunch advocate of civil liberties despite his Southern segregationist roots — said in 1974 after investigating government spying on Americans, “Each time we give up a bit of information about ourselves to the Government, we give up some of our freedom. For the more the Government or any institution knows about us, the more power it has over us. When the Government knows all of our secrets, we stand naked before official power. Stripped of our privacy, we lose our rights and privileges. The Bill of Rights then becomes just so many words.”